If you’re reading this in 2025, your source code probably lives on someone’s cloud somewhere. It might be going through an AI service or two. It might be running through a CI/CD pipeline in the cloud, steps controlled by a stranger on the Internet.
We’ve handed off control — not just where code lives, but how it moves, who can see it, and what tools we’re allowed to use. Even some self-hosted platforms may come bundled with vendor lock-in. Their issue tracker, their code review, their CI pipeline. They’re built-in and within reach, but more often than not, they’re the wrong tool for the job.
We trust these companies to be good stewards. Sometimes that works out, but sometimes that trust ages like fine milk. Platforms get acquired. Prices go up. Integrations break. Our private code leaks. Sometimes by their own AI. Once your company’s code is in their possession, you just have to hope they have your best interests at heart.
And then there’s the challenges of the world’s political climate. If your data is hosted by a cloud-based service, you don’t necessarily know where in the world it is. Data privacy agreements and laws can change unexpectedly, and what was once a safe bet might suddenly become a major liability.
So maybe it’s worth asking:
Should we take back control of our code?
And how do we start?
Choose Self-Hosted
Taking control of your own code starts with taking control over the tools you use to manage your code, your projects. And the best way to do that is to choose the right tools for your needs and host them in a network you control.
Most forms of development tools can be self-hosted, including:
- Source code repository software (e..g, Git, Perforce, Fossil, Subversion, Gitea, GitLab)
- Code review software (e..g, Review Board)
- Bug trackers (e..g, Bugzilla, Mantis, Bugasura)
- Knowledge tracking/Wikis (e.g., Mediawiki, Obsidian)
- Continuous Integration (e.g., Jenkins, Concourse)
- AI code generation (models managed by Ollama)
Some of these are all-in-one solutions, taking care of most or all aspects of development. These can be easy to set up, and will be similar to choosing a cloud solution. This can be a good option for moving your development in-house, but they do come with tradeoffs:
- You’re stuck with the limitations of the tools it provides, making it harder to swap them for more specialized (and often better) dedicated tools (such as better code review or bug trackers)
- If you ever want to switch to something new (say, a future successor to Git), you may have to find a new all-in-one tool and fully replace your old one.
Many of the standalone solutions, such as Review Board, are designed to work with a wide range of other tools and types of source code repositories. These are usually built to be extensible for any of your custom in-house needs, and are quite future-proofed. You can piece together the right tools that suit your organization, without locking yourself in to any one.
And though this means having to manage multiple tools in-house, the tradeoff is increased flexibility for your developers and products. Plus, these tools usually offer some pretty stellar support services that can work more closely with your team than any SaaS giant.
In either case, self-hosting any of these tools will help keep your source code, your discussions, your proprietary information, and your decisions private and in your control.
But there’s one more consideration.
Choose Open Source?
Self-hosted development products on the market tend to be in one of the following categories:
- Open source and free
- Closed source and paid
- A hybrid model (open source with paid support, or open source with closed source add-ons)
Some cloud providers offer paid closed-source versions of their products to run in your network, though they’re still a black box. You don’t always know if any of your data’s leaving your network, and you’re stuck with the feature set and the lifespan of the product. If the product is discontinued, you have little choice but to find an alternative once again.
On the other side are open source products that are fully community-driven. The code is in your control, and if the product’s ever discontinued, you can fork and patch as needed. However, it may not come with support, so you’re on your own.
Hybrid models give you the best of both. Open source code that you can verify and tailor to your needs, with the option of business-class support to help you manage the product so that you can spend more time focusing on your own code. Paid offerings often include premium features or enhancements that make the product even more useful for teams with growing or specialized needs.
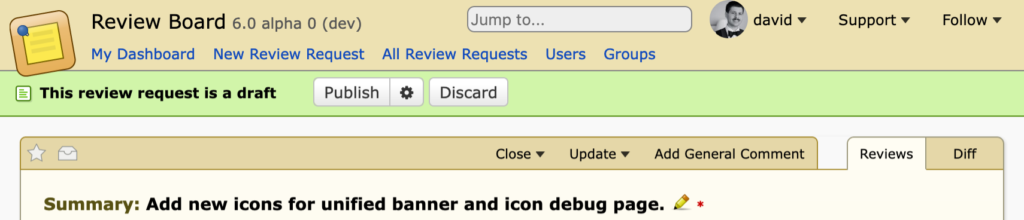
Hybrid is the model we use with Review Board, with paid support and extra features via Power Pack.
An Incomplete List of Self-Hosted Products
The beauty of these products is that they’re not just clones of GitHub. There’s a lot of features and innovation out there to explore.
Here’s a few of the options available for projects today. If you know of a good one that should be included in this list, we’d love to hear about it!
Source Code Management:
- Git — Open source — Decentralized version control system.
- GitLab — Open source with paid support — Offers both free and enterprise self-hosted editions.
- Gitea / Forgejo — Open source — Lightweight Git hosting platforms, simple to self-host.
- GitHub Enterprise Server — Closed source — GitHub’s paid, self-hosted enterprise edition.
- Perforce (Helix Core) — Closed source — High-performance version control for large codebases.
- Fossil — Open source — DVCS with built-in wiki, issue tracking, and web UI.
- Subversion (SVN) — Open source — Centralized version control system.
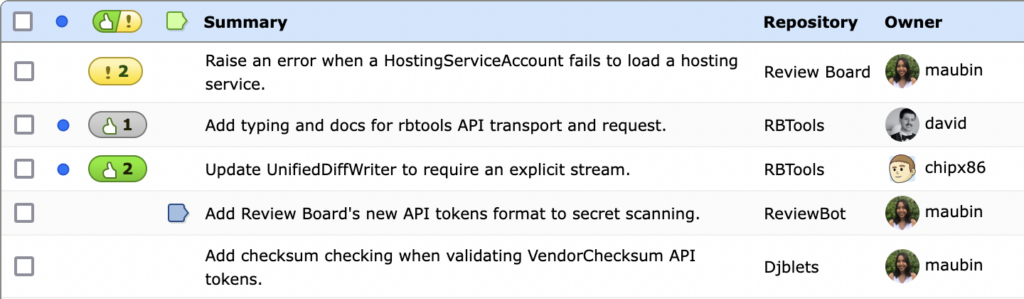
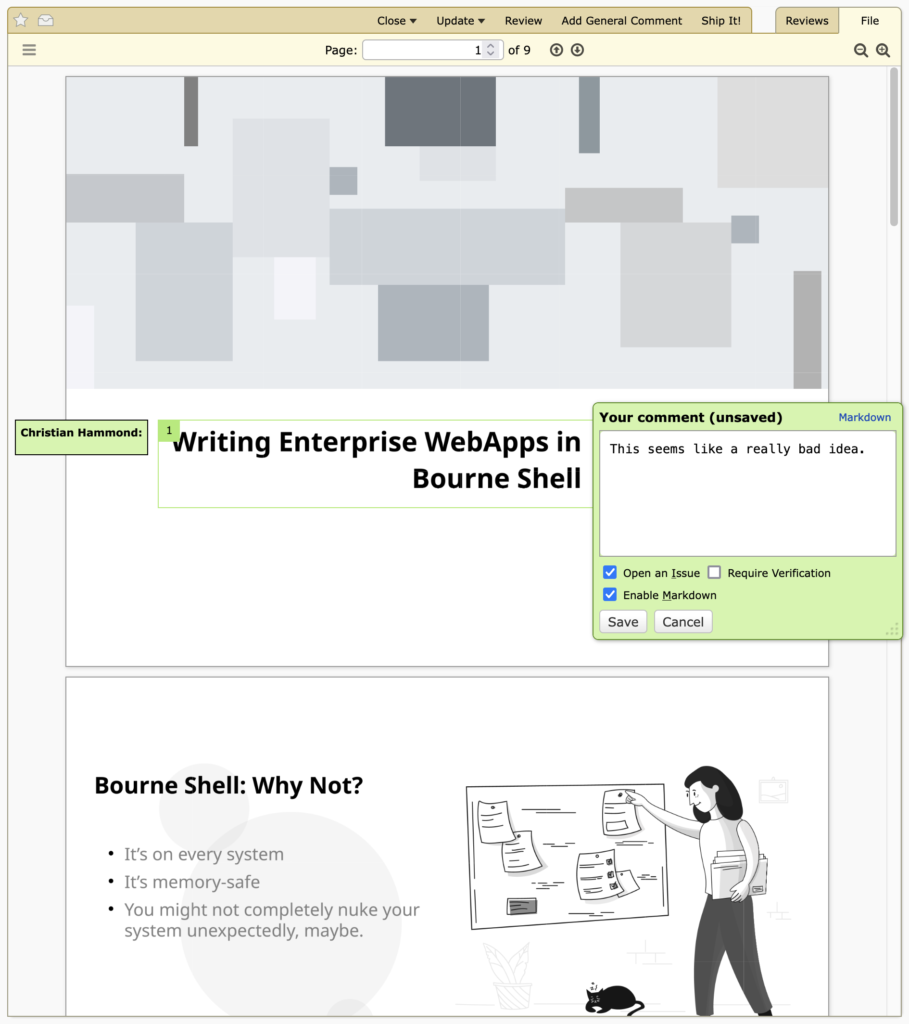
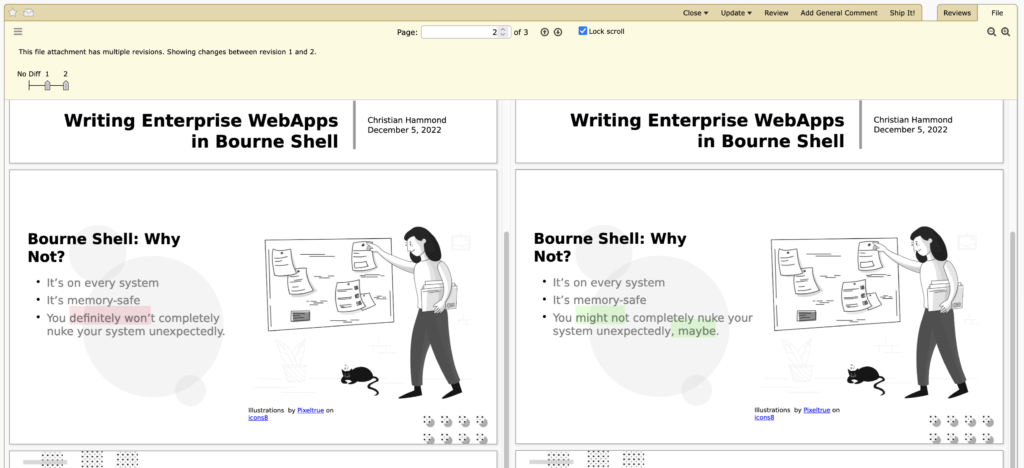
Code Review:
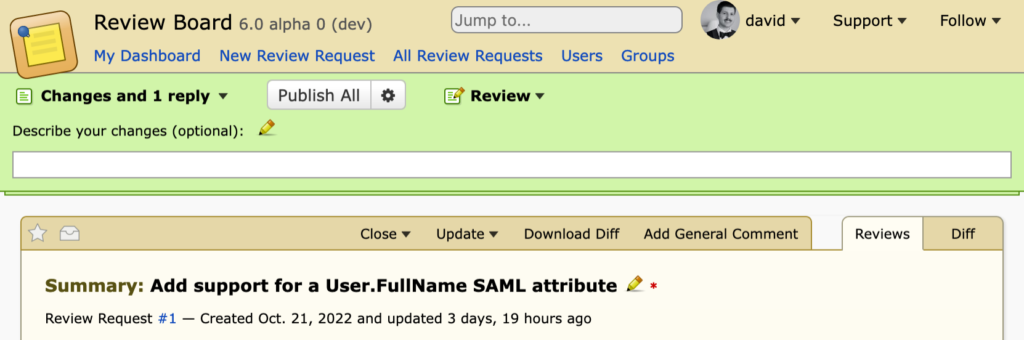
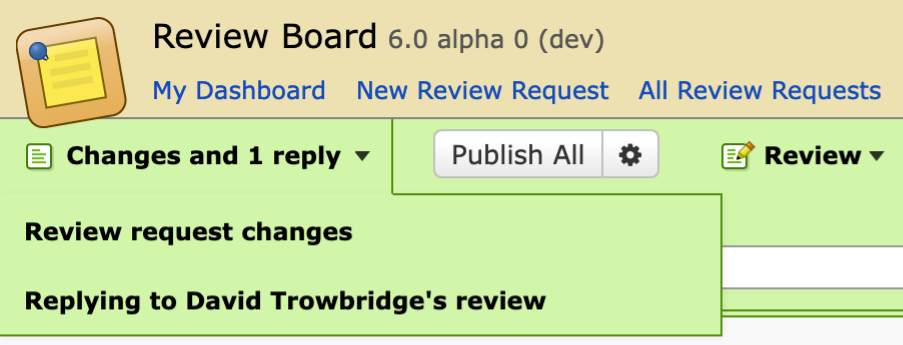
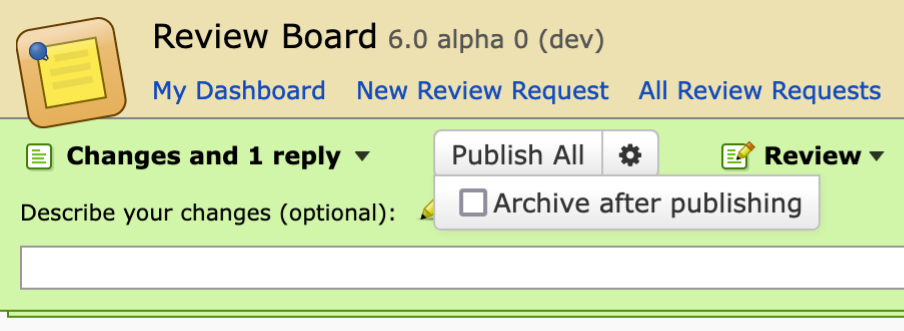
- Review Board — Open source with paid support and licensed add-ons — Code review tool with repository and diff support.
- Phorge — Open source — Community-maintained fork of the retired Phabricator platform.
- Gerrit — Open source — Advanced Git code review system, used by large orgs like Android.
- GitLab — Open source with paid support — Built-in code review features.
- Gitea / Forgejo — Open source — Lightweight code hosting with basic pull request-style review.
Bug Trackers:
- Bugzilla — Open source — Mature bug tracking system with strong customization.
- MantisBT — Open source — Lightweight bug tracker with a web interface.
- Redmine — Open source — Project management tool with issue tracking and Gantt charts.
- Trac — Open source — Combines bug tracking, wiki, and SCM integration.
- Bugasura — Hybrid (self-hosted plan) — Modern, UX-focused issue tracker.
- YouTrack — Closed source — JetBrains’ tracker with on-prem options.
Knowledge Tracking / Wikis:
- MediaWiki — Open source — Powers Wikipedia; highly customizable and scalable.
- BookStack — Open source — User-friendly documentation/wiki platform.
- DokuWiki — Open source — File-based wiki, great for small teams or personal use.
- Outline — Open source — Modern wiki with markdown support and rich integrations.
- Trac — Open source — Includes a built-in wiki with developer-focused features.
- Obsidian — Closed source with local-first design — Markdown knowledge base that can run fully offline.
Continuous Integration / Delivery:
- Jenkins — Open source — Powerful CI/CD automation with vast plugin support.
- Concourse CI — Open source — Pipeline-focused CI/CD system with strong reproducibility.
- Buildbot — Open source — Flexible Python-based build system for complex workflows.
- Drone CI — Open source — Container-native CI/CD with YAML-based config.
- Woodpecker CI — Open source — Community-driven fork of Drone with active development.
- GitLab CI — Open source with paid support — Integrated CI/CD in GitLab.
AI Code Assistance (Local Models):
- Ollama — Open source with prebuilt models — Run LLMs like Code Llama, StarCoder locally.
- LM Studio — Closed source (free) — GUI for downloading and running local LLMs.
- Tabby — Open source — Self-hosted AI code assistant compatible with VS Code, JetBrains.
- CodeGeeX — Open source (model weights available) — AI code generation with local inference support.
Take Back Control
There’s no shortage of excellent tools out there. You don’t need to settle for trusting your code, your infrastructure, or your future to companies that may not share your priorities (and increasingly see your hard work as little more than AI training data). Owning your development stack isn’t just a matter of principle. It’s a safeguard. An investment in your future. One you can start building today.